Online Privacy
Brief Description
The purpose of this research is to provide a common
framework for communicating and discussing privacy issues. To achieve this
objective, the concept of an Information Privacy Unit (IPU) was introduced where
all the possible ways of addressing privacy concerns were incorporated. This led
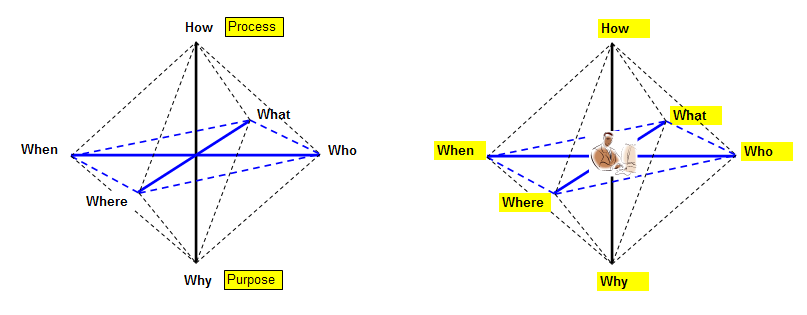
to viewing privacy instances as a point in a six-dimensional space composed of
the six interrogatives of the English language (What, When, Who, Where, Why and
How). This approach can also be used to define guidelines for
implementing privacy policies in software that act as mediators (browsers) or as
representatives (clients, servers) of interacting entities.
The Information Privacy Unit (IPU) is defined as follows;
Although we might not be able to ask all the possible questions regarding and information exchange that involves ownership and process of some personal data we can definitely address all the possible ways questions will be expressed. Having a common language is a vital means of dealing with conflicts and misunderstandings.
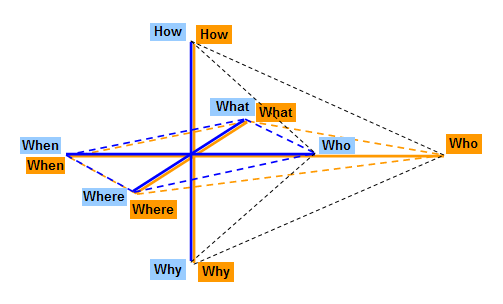
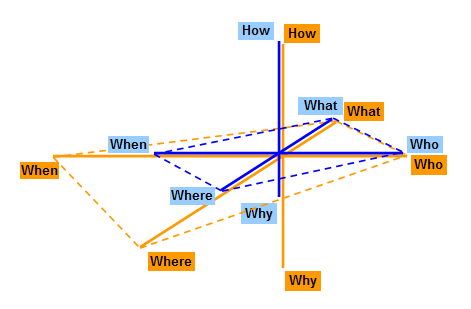
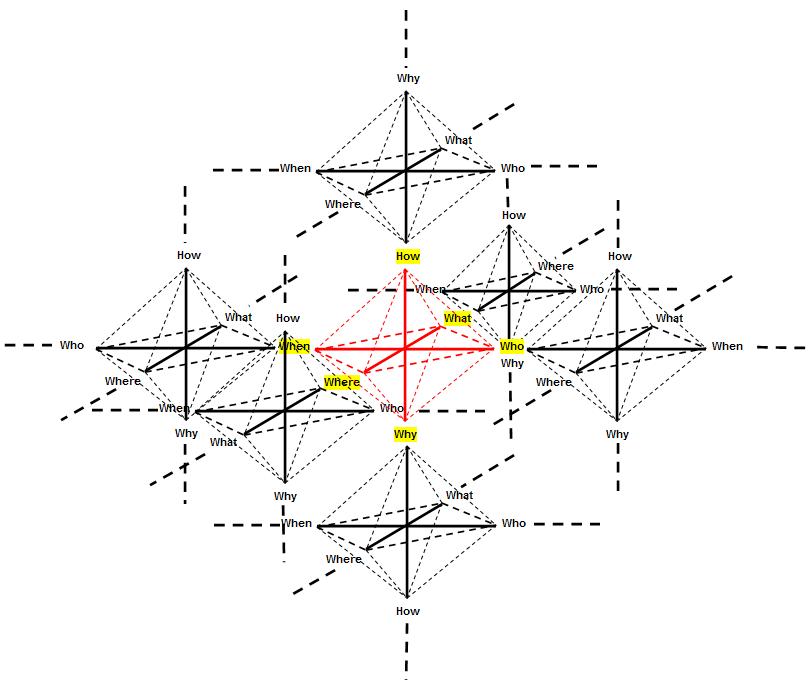
Since conflicts arise when many entities get involved, the actual situation looks more like:
Case study
In an "ideal" situation we have have something like:
When there is a violation in some
dimension it becomes: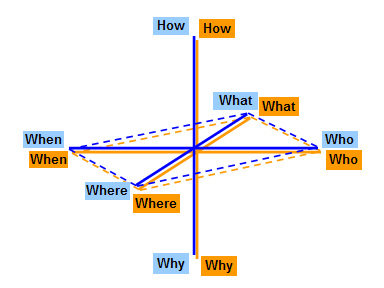
The online
surfer might believe that he gives ownership to the web site requesting
the personal data while the web site might share ownership with its
affiliates. Clearly this constitutes a misunderstanding of the
Who dimension. When there is a violation in three
dimensions it could become:
Presentations The following presentation was given at the
IBLT 2006 Conference in Copenhagen.
A Six Dimensional
Approach to Online Privacy Presentations The corresponding paper appeared in
Int. J. of
Technology Transfer and Commercialization,
6,1, 56-63, 2007. Contact
Nicholas Harkiolakis, PhD
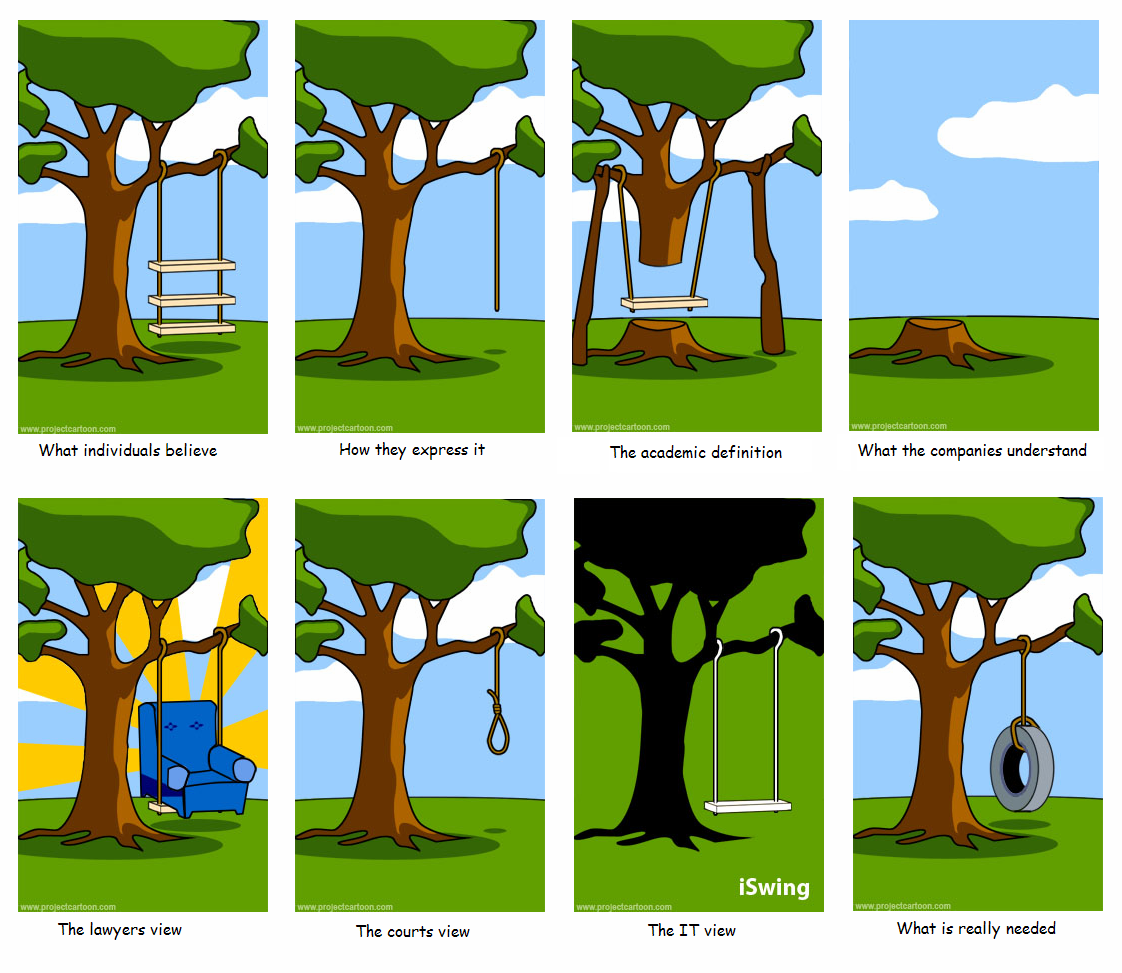
for more information on this project. Bellow is my adaptation for privacy related issues
of one of longest lasting cartoons in IT/Project Management. The first time I
saw it in its original form was 1978.
Perceptions of Privacy (the funny way)